Vendor due diligence in cybersecurity
Financial institutions must conduct thorough vendor due diligence to mitigate cybersecurity risks. This article provides a step-by-step checklist for effective vendor assessment.
-
Nikita Alexander
- April 22, 2025
- 7 minutes

Financial institutions operate within a complex ecosystem, relying heavily on a network of third-party vendors to provide various essential services. This reliance introduces inherent cybersecurity risks, making vendor due diligence a critical and indispensable component of any robust cybersecurity risk management program. Thorough and comprehensive vendor due diligence enables financial institutions to proactively assess the potential risks associated with engaging a specific vendor, allowing them to make well-informed decisions, mitigate potential threats, and establish secure and resilient vendor relationships. This article provides a detailed, step-by-step checklist designed to guide financial institutions in conducting effective vendor due diligence.
Why is vendor due diligence important?
Vendor due diligence is not merely a procedural formality; it’s a fundamental security practice that offers several key benefits for financial institutions:
- Risk identification: Vendor due diligence is crucial for proactively identifying potential cybersecurity risks inherent in a vendor’s security practices, their handling of sensitive data, and their overall operational resilience. This process helps financial institutions understand the potential vulnerabilities and threats that engaging a particular vendor might introduce into their environment.
- Compliance assurance: In the highly regulated financial sector, vendor due diligence plays a vital role in ensuring that vendors comply with all relevant regulations and industry standards. This helps financial institutions meet their own compliance obligations and avoid potential legal and financial penalties.
- Data protection: Given the sensitive nature of financial data, vendor due diligence is essential for verifying that vendors have implemented adequate safeguards and controls to protect this information throughout its lifecycle. This includes measures to secure data during storage, transmission, and processing.
- Informed decision-making: Ultimately, thorough vendor due diligence provides financial institutions with the comprehensive information and insights necessary to make informed and strategic decisions about whether to engage a vendor and, if so, under what specific conditions and security requirements.
Vendor due diligence checklist:
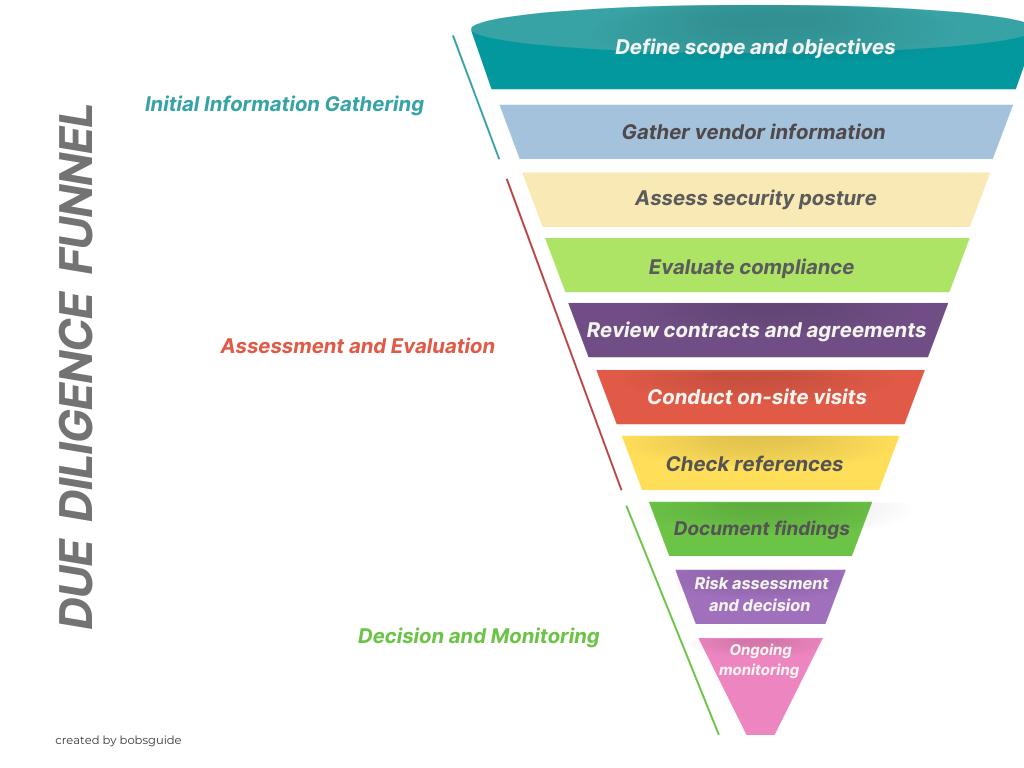
Here’s a detailed, step-by-step checklist to guide financial institutions in conducting effective vendor due diligence:
-
Define scope and objectives:
- Clearly and precisely define the scope and specific objectives of the vendor due diligence process. This involves outlining the boundaries of the assessment and the key questions that need to be answered.
- Identify and document the specific services that the vendor will be providing to the financial institution. This includes a detailed understanding of the vendor’s role and responsibilities.
- Identify the specific types of data that the vendor will have access to, process, or store. This is crucial for assessing potential data-related risks.
-
Gather vendor information:
- Request and obtain relevant documentation and information from the vendor. This may include:
- Security policies and procedures: Documentation outlining the vendor’s approach to security.
- Security certifications and attestations: Evidence of compliance with industry standards (e.g., ISO 27001, SOC 2).
- Audit reports: Independent assessments of the vendor’s security controls.
- Incident history: Information about past security incidents experienced by the vendor.
- Organizational structure and ownership: Details about the vendor’s company and its ownership.
- Financial stability information: To assess the vendor’s ability to operate reliably.
- Request and obtain relevant documentation and information from the vendor. This may include:
-
Assess security posture:
- Thoroughly evaluate the vendor’s overall security posture. This involves a detailed examination of:
- Security controls: The specific security measures implemented by the vendor (e.g., access controls, encryption, network security).
- Vulnerability management practices: The vendor’s processes for identifying, assessing, and patching vulnerabilities.
- Incident response capabilities: The vendor’s plan and capabilities for responding to security incidents.
- Security awareness training: Programs to educate vendor employees about security best practices.
- Physical security: Measures to protect the vendor’s facilities and equipment.
- Thoroughly evaluate the vendor’s overall security posture. This involves a detailed examination of:
-
Evaluate compliance:
- Assess the vendor’s compliance with all relevant regulations and industry standards that apply to the financial institution and the services being provided.
- This may include regulations such as:
- GDPR (General Data Protection Regulation): If handling data of EU residents.
- CCPA (California Consumer Privacy Act): If handling data of California residents.
- GLBA (Gramm-Leach-Bliley Act): In the United States.
- PCI DSS (Payment Card Industry Data Security Standard): If handling cardholder data.
- DORA (Digital Operational Resilience Act): In the EU.
-
Review contracts and agreements:
- Carefully and meticulously review all contracts and service level agreements (SLAs) with the vendor.
- Ensure that these agreements include:
- Appropriate cybersecurity clauses: As outlined in Article 8.
- Clear data protection provisions: Detailing how data will be handled and protected.
- Liability clauses: Defining responsibilities in case of security breaches.
- Audit rights: Granting the financial institution the right to audit the vendor’s security.
- Incident reporting requirements: Specifying how the vendor must report security incidents.
-
Conduct on-site visits (if necessary):
- Determine if on-site visits to the vendor’s facilities are necessary and feasible.
- On-site visits may be warranted for vendors providing critical services or handling highly sensitive data.
- During on-site visits, assess:
- Physical security controls: Measures to protect facilities and equipment.
- Operational practices: Security procedures and employee behavior.
-
Check references:
- Request and check references from other clients of the vendor.
- Gather feedback on:
- The vendor’s security track record.
- Their reliability and service quality.
- Their responsiveness to security issues.
-
Document findings:
- Thoroughly and accurately document all findings, observations, and supporting evidence from the due diligence process.
- This documentation should be organized and easily accessible for review and decision-making.
-
Risk assessment and decision:
- Conduct a comprehensive risk assessment based on the findings of the vendor due diligence.
- Evaluate the identified risks in terms of their likelihood and potential impact on the financial institution.
- Make a well-informed decision about whether to engage the vendor.
- If engaging the vendor, determine any specific security requirements or conditions that must be met.
-
Ongoing monitoring:
- Establish a robust process for ongoing monitoring of the vendor’s security performance and compliance throughout the duration of the relationship.
- This may include:
- Periodic security assessments.
- Review of security reports and logs.
- Monitoring of service level agreements (SLAs).
- Staying informed about any changes in the vendor’s security posture.
Key areas of focus
When conducting vendor due diligence, financial institutions should place particular emphasis on the following key areas:
-
Security controls:
- Thoroughly evaluate the vendor’s implementation and effectiveness of security controls.
- This includes:
- Access controls: Measures to restrict access to systems and data.
- Encryption: Technologies to protect data confidentiality.
- Vulnerability management: Processes for identifying and addressing vulnerabilities.
- Network security: Measures to protect the vendor’s network infrastructure.
- Data loss prevention (DLP): Technologies to prevent data exfiltration.
-
Data protection:
- Carefully assess the vendor’s policies and procedures for protecting sensitive data.
- This includes:
- Data storage: How data is stored and secured.
- Data transmission: How data is transmitted and protected during transit.
- Data processing: How data is processed and accessed.
- Data disposal: How data is securely disposed of when no longer needed.
- Data retention: How long data is retained and the justification for retention periods.
-
Incident response:
- Thoroughly review the vendor’s incident response plan and their demonstrated ability to effectively respond to and recover from security incidents.
- Assess:
- Incident detection capabilities: How the vendor detects security incidents.
- Containment procedures: How the vendor contains the impact of an incident.
- Eradication methods: How the vendor removes threats and restores systems.
- Communication protocols: How the vendor communicates during an incident.
- Recovery processes: How the vendor restores operations and data.
-
Business continuity:
- Evaluate the vendor’s business continuity and disaster recovery plans to ensure they can maintain service availability in the event of disruptions.
- Assess:
- Backup and recovery procedures: How data and systems are backed up and recovered.
- Failover capabilities: The vendor’s ability to switch to backup systems.
- Redundancy: The level of redundancy in the vendor’s infrastructure.
- Testing of plans: How often the vendor tests their business continuity plans.
-
Compliance:
- Thoroughly verify the vendor’s compliance with all relevant regulations and industry standards.
- Ensure that the vendor can meet the financial institution’s compliance obligations.
- Obtain evidence of compliance, such as certifications and audit reports.
Vendor due diligence is not a one-time event but rather an ongoing and essential process for financial institutions to effectively manage the complex cybersecurity risks associated with third-party vendors. By diligently following a comprehensive step-by-step checklist, focusing on key areas of risk, and maintaining continuous monitoring, financial institutions can make well-informed decisions, establish secure vendor relationships, and protect their valuable assets and reputation in an increasingly interconnected and threat-prone environment.